Vendor News
Amazic IT Channel Magazine
Login to your Account
Create Affiliate Account
Trouble Signing In?
Enter your email below to request a Reset Password Link
-
Is It Time to Migrate? A Practical Look at Kubernetes Ingress vs. Gateway API
Still battling Kubernetes Ingress complexities? Discover why it's time to migrate! This guide unpacks the limitations of traditional Ingress and reveals how the Kubernetes Gateway API, implemented by Calico Ingress Gateway with Envoy proxy, offers a standardized, role-aware, and feature-rich solution for secure, streamlined traffic management.
-
Kubernetes Cost Optimization: From Roadblocks to Results
Discover how Trax, a leader in retail technology, leveraged PerfectScale to overcome manual Kubernetes optimization roadblocks, achieving an astounding 75% cost reduction in one cluster (saving over 6-figures annually) and significantly improving their "cost per processing" metric by gaining granular visibility and actionable insights across their multi-cloud, multi-cluster AWS EKS environment.
-
Leading Global FinTech's DynamoDB Cost Optimization with PointFive
A global FinTech giant partnered with PointFive to uncover hidden inefficiencies in their DynamoDB usage. With deep waste detection and actionable recommendations, they reduced storage costs by 60% for key tables and eliminated waste from inactive data—achieving significant savings in just 10 days without slowing innovation.
-
Leveraging Devtron for Secure CI/CD Pipelines
Devtron bakes security into CI/CD pipelines—blocking vulnerabilities, enforcing policies, and automating compliance without slowing deployments. Kubernetes-native, audit-ready, and trusted by enterprises.
-
LoRaWAN Explained: Protocol, Perks, and Use Cases
Unpack LoRaWAN: the low-power, long-range protocol powering the IoT revolution! Discover its unique features, star-of-stars architecture, and diverse applications from smart cities to industrial automation. Learn how it delivers cost-effectiveness, scalability, and enhanced connectivity, and how Netmaker boosts its network security.
-
Making the Most of Your Docker Hardened Images Trial – Part 1
Start your DHI trial strong! This guide shows how Docker Hardened Images move you to near-zero CVEs in 3 steps. We compared official Node.js to DHI and found a 100% vulnerability elimination (25 CVEs to 0), a 90% package reduction, and 41% smaller images, validating the compliance benefits with Docker Scout and SBOMs.
Format: ArticleTopic: Best PracticesContent Type: Community Content -
MariaDB Migration Assessment Tool: How Ready Are You to Migrate to MariaDB from Oracle?
Discover how the MariaDB Migration Assessment Tool simplifies the process of migrating from Oracle Database to MariaDB. Learn how it analyzes your Oracle schema, identifies compatibility issues, and provides actionable insights to ensure a smooth, cost-effective migration.
-
Master API security: Securing your entire API ecosystem with Beagle Security’s API discovery
Discover how unchecked API sprawl creates critical security blind spots for fast-growing fintech startups, leading to data breaches and operational inefficiencies. Learn how Beagle Security's API discovery feature automatically uncovers and tests all APIs within Kubernetes or Istio environments, ensuring complete visibility and proactive vulnerability management.
-
Meet the application security platform built for the AI era
The era of vibe coding is here. Learn how Endor Labs is helping AppSec teams secure and fix AI-generated code with a new agentic AI platform.
-
Memorial Care Securely Elevates Communication Standards and Boost Efficiency with Grammarly
MemorialCare needed a solution to improve internal communication without compromising patient data. Discover how they leveraged Grammarly's HIPAA-compliant enterprise product to centralize communication, save over 20 days per employee annually on revisions, and boost confidence across their growing healthcare workforce.
Format: ArticleTopic: Software/ ToolsContent Type: Editorial Content -
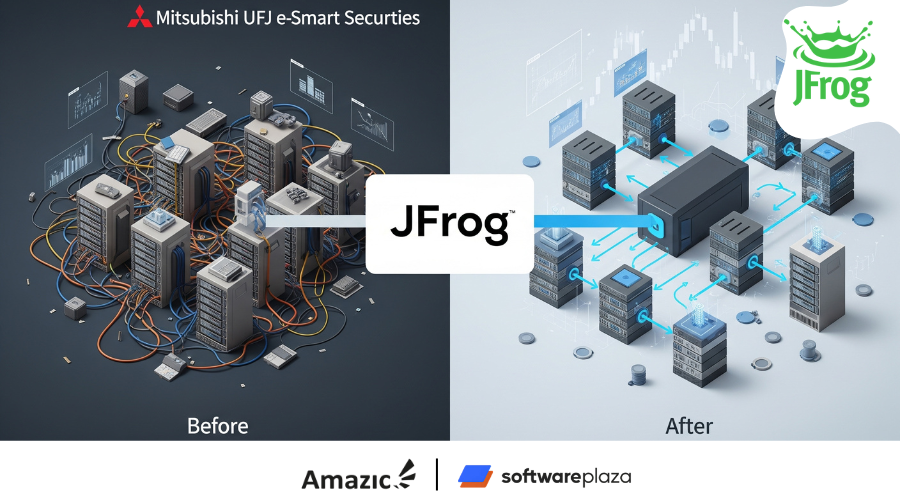
Mitsubishi UFJ e-Smart Securities Optimizes Package Management and Automates Deployment with JFrog
Mitsubishi UFJ e-Smart Securities has historically faced challenges around optimizing deployment and package management. By adopting the JFrog Software Supply Chain Platform, the company has transformed its approach to DevOps and realized significant improvements in security, efficiency, and speed.
-
Mysten Labs Improves DevEx with Endor Labs
Discover how Mysten Labs, pioneers of the Sui blockchain, transformed their AppSec by ditching an unreliable tool for Endor Labs. Learn how they achieved trusted findings, minimal developer friction, and faster remediation, enabling them to build the world's most secure blockchain.