Vendor News
Amazic IT Channel Magazine
Login to your Account
Create Affiliate Account
Trouble Signing In?
Enter your email below to request a Reset Password Link
-
Why Is Third-Party Risk Management So Important
In today’s interconnected world, a business is only as strong as its weakest vendor. Third-party risk management (TPRM) is essential for safeguarding sensitive data, ensuring regulatory compliance, and maintaining operational continuity. By proactively assessing and monitoring vendors—using strategies and tools like Cyble’s TPRM solutions—organizations can turn potential vulnerabilities into strengths, build trust, and secure long-term success.
-
Why Policy as Code is a Game Changer for Platform Engineers
Policy as Code (PaC) is transforming platform engineering by embedding security, compliance, and governance directly into developer workflows. It empowers developers with faster feedback, enables secure self-service, ensures consistent environments, and automates policy enforcement—boosting efficiency and scalability. By shifting policy management to code, teams gain transparency, reduce errors, and streamline compliance, paving the way for more secure, scalable, and developer-friendly platforms. The future of internal developer platforms is Policy as Code.
-
Why SBOM Took Center Stage at KubeCon 2025: The Future of Software Supply Chain Security
Explore why SBOM was the biggest topic at KubeCon 2025. Learn how Anchore Syft and CycloneDX/SPDX standards are redefining Kubernetes software supply chain security.
-
Why Security Policies Frustrate Developers (and How We Can Fix Them)
Most security policies create more problems than they solve, overwhelming developers with noise and unnecessary build breaks. Here's what a better approach looks like.
-
Why Top Spanish Business School Esade Migrated from MySQL to MariaDB Enterprise Server
sade Ramon Llull University, a top business school, sought a robust database solution to support their critical eLearning platform, Moodle, and its 7,000 students and 1,000 daily concurrent users. Facing poor performance and low availability with MySQL community edition, they chose MariaDB Enterprise Server with Galera Cluster for its high query speed, robust clustering, and comprehensive support, drastically improving Moodle's performance and student experience.
-
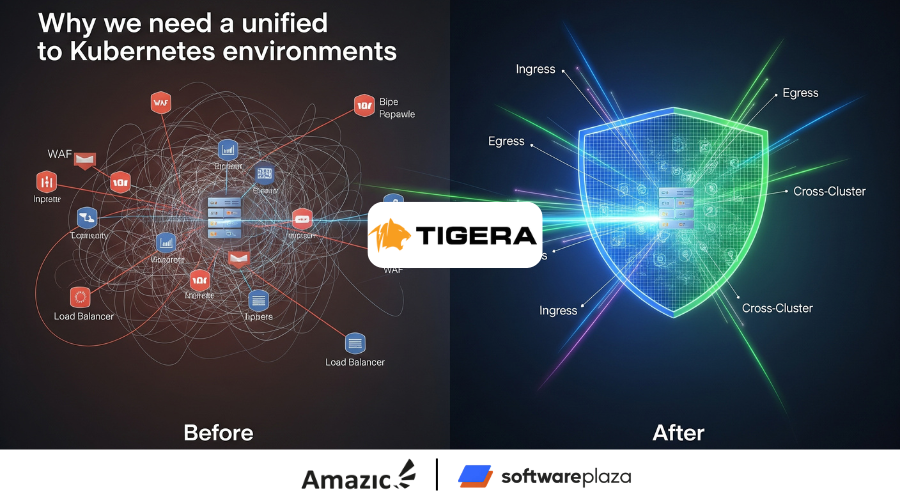
Why we need a unified approach to Kubernetes environments
Tired of Kubernetes networking chaos? Discover why fragmented tools lead to operational overhead, hidden costs, and security gaps. Learn how a unified approach to Kubernetes networking and security eliminates tool sprawl, enhances threat detection, and drives better outcomes for your modern applications.
-
Work Smarter, Not Harder: AKS Cluster Deployment and Maintenance With Palette
Managed Kubernetes services like AKS may simplify cluster deployment, but they still leave you managing complex infrastructure tasks. This article explores how Spectro Cloud Palette streamlines Azure Kubernetes Service operations—automating configuration, scaling, monitoring, and security—so you can enjoy the benefits of AKS without the operational headaches.
Format: ArticleTopic: Software/ ToolsContent Type: Community Content -
Workload Identity Meets Supply Chain Security: Teleport's Sigstore Integration
Modern software supply chains face increasing complexity and risk, especially from supply chain attacks like SUNBURST. This article explores how Sigstore and Teleport's Machine & Workload Identity can fortify your CI/CD pipeline. Learn how Sigstore enables keyless, verifiable artifact signing, and how Teleport integrates these signatures into workload attestation using SPIFFE-based SVIDs. Discover how to enforce policies that block compromised containers from accessing sensitive resources, and how cryptographic identity can replace static secrets for secure service-to-service communication. A must-read for DevSecOps teams aiming to embed security into the development lifecycle.
-
Zebra Technologies Cuts SCA Noise by 97% with Endor Labs
Discover how Zebra Technologies transformed its Product Security by adopting Endor Labs, slashing SCA alert noise by an astounding 97% and reducing remediation effort by over 60%. Learn how they achieved accurate risk prioritization and boosted developer buy-in for a truly proactive security model.