Vendor News
Amazic IT Channel Magazine
Login to your Account
Create Affiliate Account
Trouble Signing In?
Enter your email below to request a Reset Password Link
-
The new DeepL security features enabling fully compliant innovation with Language AI
Security vs. innovation? Get both with DeepL! Discover 7 new security features, including Bring Your Own Key encryption and Multi-factor authentication, that empower enterprises to prevent "Shadow AI" and innovate with Language AI while meeting strict standards like ISO 27001, SOC 2, and HIPAA.
-
The Shadow AI Crisis: Why Enterprise Governance Can’t Wait Any Longer
The Shadow AI Crisis: Why Enterprise Governance Can’t Wait – With over 70% of AI use happening outside IT’s control, shadow AI is creating massive security, compliance, and visibility risks. As unofficial tools proliferate, the need for enterprise-ready governance is urgent. Learn how forward-thinking organizations are turning this underground trend into a competitive advantage with smarter platforms, embedded security, and real-time oversight.
-
The state of observability in 2025: a deep dive on our third annual Observability Survey
Dive into Grafana Labs' third annual Observability Survey for 2025! Uncover how observability practices are maturing, why traces are gaining traction, the enduring power of open source, the emerging role of AI, and how cost continues to drive tool selection across organizations of all sizes.
-
The state of observability in 2025: a deep dive on our third annual Observability Survey
Dive into Grafana Labs' third annual Observability Survey for 2025! Uncover how observability practices are maturing, why traces are gaining traction, the enduring power of open source, the emerging role of AI, and how cost continues to drive tool selection across organizations of all sizes.
-
The ten pillars of pragmatic deployments
At Octopus, we've distilled years of deployment experience into the 10 Pillars of Pragmatic Deployments — a flexible, experience-driven framework to help teams build reliable, repeatable, and user-friendly software deployments. From understanding repeatable and verifiable deployments to achieving seamless cutovers with smart strategies like rolling updates and canary deployments, this guide walks you through modern deployment best practices that work in the real world — not just in theory.
-
The use of AI has become the expectation, Are you keeping up?
Is AI truly reflexive in your company? Discover why saying "no" to AI multiplies risk and how secure, owned AI solutions like Civo's relaxAI can boost productivity, improve decision quality, and transform your organizational culture, ensuring your teams harness AI without sacrificing control or compliance.
-
Top 15 Kubectl plugins for security engineers in 2025
Kubernetes security is evolving fast—and so should your tools. This roundup of the top kubectl plugins for 2025 spotlights essential extensions that help security teams audit RBAC, trace runtime activity, manage secrets securely, and respond to threats in real time. Whether you're managing complex clusters or chasing compliance, these plugins supercharge your command line with the visibility and control you need.
-
Top 5 features to look for in a cloud detection and response solution
Cloud detection and response (CDR) is essential for securing modern hybrid and multicloud environments, where traditional tools fall short. This article explores the key challenges facing security teams—like lack of runtime visibility, alert fatigue, and skill gaps—and outlines how purpose-built CDR solutions like Sysdig address them. From real-time visibility and automated threat correlation to AI-powered threat investigation, discover what to look for in a CDR platform that delivers speed, context, and control across your entire cloud infrastructure.
-
Troubleshooting Kubernetes with AI: Using the K8s MCP server
Unlock AI-powered Kubernetes troubleshooting! Discover the Model Context Protocol (MCP) and how it standardizes AI agent interactions with Kubernetes tools like kubectl, Helm, and ArgoCD. Learn how to integrate K8s MCP Server with agentic frameworks like PydanticAI for seamless, context-rich cluster management.
-
Turning Migration Into a Strategic Advantage
For fintechs, trust depends on uptime — every transaction must work flawlessly. This article explores how financial technology companies can migrate to AWS without downtime, protecting both performance and reputation. Discover resilience-first strategies like automation, blue/green deployments, and compliance-by-design that turn cloud migration into a strategic advantage rather than a risk.
Format: VideoTopic: Best PracticesContent Type: Community Content -
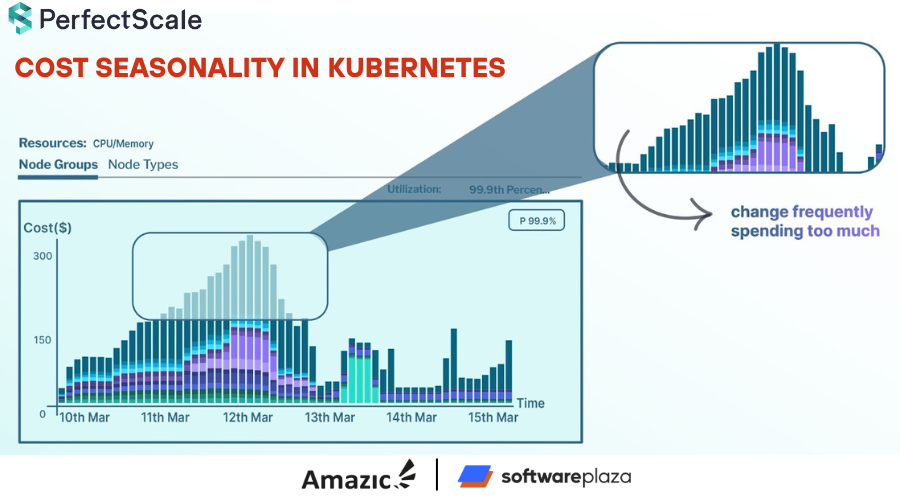
Understanding Cost Seasonality in Kubernetes
Unpack the concept of cost seasonality in Kubernetes, explore the factors that drive its fluctuations, and discover effective strategies—including right-sizing, autoscaling optimization, and leveraging tools like PerfectScale—to manage and predict your cloud spend while maintaining performance.
-
Understanding Kubernetes Commands and Arguments
Want to customize what runs inside your Kubernetes containers? This blog shows you how to use commands and arguments to override Docker defaults, with practical examples and use cases like running startup scripts and testing network connectivity.